Master NY DFS Cybersecurity Compliance in the United States
Key Takeaways
Foreign financial institutions with New York branches face strict regulatory enforcement under the New York Department of Financial Services (NYDFS) Cybersecurity Regulation, known as Part 500. Compliance requires localized risk management, immediate incident reporting, and direct executive accountability. Protecting "Nonpublic Information", which includes proprietary business data, personal identifiers, and healthcare information, is the core objective of the framework.
- Institutions must map their existing global frameworks like GDPR to the specific technical requirements of NYDFS Part 500.
- Covered entities must report qualifying cybersecurity events to the NYDFS within a strict 72-hour window.
- Failing to enforce third-party vendor risk management is a leading cause of severe regulatory penalties.
- The board of directors or a senior officer must submit an annual certification of compliance by April 15.
- A qualified Chief Information Security Officer (CISO) must oversee the program and maintain a localized incident response plan.
NYDFS Part 500 Compliance Checklist for Foreign Branches

Building a compliant cybersecurity program requires translating global corporate policies into localized New York operations. Foreign banks and financial services must implement specific technical and administrative safeguards to protect nonpublic information.
- Appoint a CISO: Designate an internal or virtual CISO responsible for overseeing the New York branch's cybersecurity program.
- Assess local risk: Perform a localized, documented risk assessment of the New York branch's specific information systems to inform the program design.
- Require MFA: Enforce multi-factor authentication for any individual accessing the entity's internal networks from an external network and for privileged local access.
- Draft response protocols: Create an incident response plan designed to promptly manage and recover from any material cybersecurity event affecting New York operations.
- Establish vendor policies: Develop written guidelines outlining the minimum cybersecurity practices required for all third-party service providers accessing the branch's data.
- Train local employees: Provide annual cybersecurity awareness training tailored to the specific threats faced by New York branch personnel.
Mapping NYDFS Part 500 Requirements to GDPR
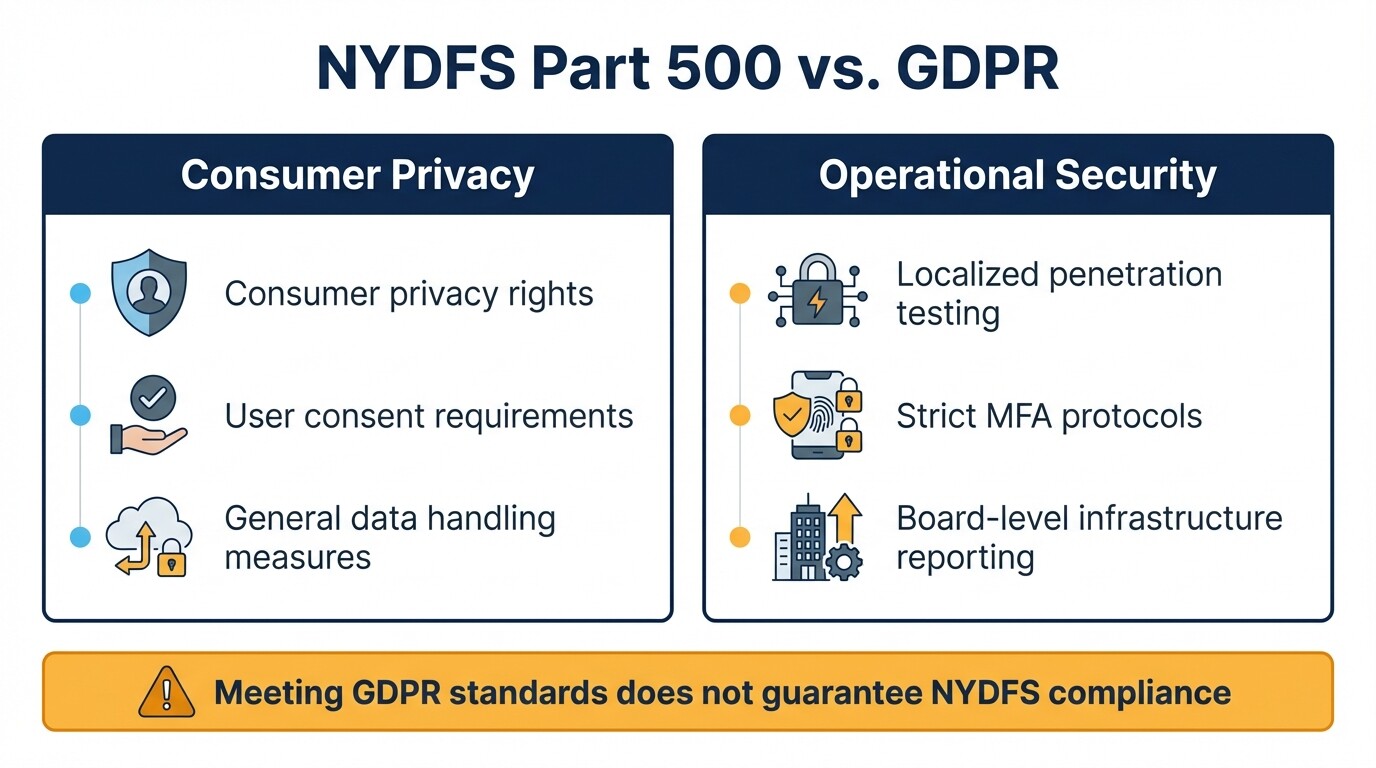
NYDFS Part 500 and the European General Data Protection Regulation (GDPR) both mandate rigorous data protection. However, they approach the issue from different regulatory angles.
GDPR focuses heavily on consumer privacy rights, user consent, and personal data handling. In contrast, NYDFS Part 500 regulates the operational security of information systems. A foreign bank cannot simply copy its GDPR compliance manual for its New York branch. Part 500 requires localized penetration testing, strict multi-factor authentication protocols, and board-level reporting specifically regarding the New York entity's infrastructure. Corporate counsel must translate GDPR's broad "technical and organizational measures" into the specific, audit-ready technical mandates found in the NYDFS rules.
The 72-Hour Cybersecurity Event Reporting Timeline
Covered entities must report qualifying cybersecurity events to the NYDFS Superintendent within 72 hours of determining that a reportable event occurred. This timeline is legally binding and leaves almost no room for administrative delays.
The 72-hour clock begins the moment the institution determines an event meets the regulatory threshold. It does not wait until the internal investigation concludes. Reportable incidents include events triggering notice requirements to other government bodies or self-regulatory agencies. The rule also covers events likely to materially harm normal business operations. Foreign institutions must use the official NYDFS Cybersecurity Portal to submit these time-sensitive notices.
Appointing a CISO and Localized Incident Response
Every foreign financial institution with a New York branch must designate a qualified Chief Information Security Officer (CISO) to enforce the cybersecurity program. The CISO must develop and maintain an incident response plan tailored to the New York branch's specific infrastructure and operational realities.
The CISO does not need to be a direct employee of the New York branch. Foreign institutions frequently use a parent company executive or a third-party service provider. The designated individual must have clear authority over the local branch's systems and report annually to the branch's governing body on material cybersecurity risks. The incident response plan they oversee must define internal processes for responding to an attack. It must also clarify local leadership roles during a crisis and establish external communication strategies.
Third-Party Vendor Risk Management
Foreign banks face severe DFS penalties for neglecting third-party vendor risk management. Covered entities must implement written policies that evaluate, audit, and monitor the cybersecurity practices of any vendor accessing their systems.
Many cyber breaches originate from vulnerable external service providers rather than internal systems. NYDFS requires institutions to perform rigorous due diligence before onboarding a vendor and to periodically assess their security posture afterward. The written policy must establish minimum cybersecurity requirements for vendors, mandate encryption protocols for data in transit and at rest, and outline how the vendor will notify the financial institution after a breach.
Annual Certification of Compliance Deadlines
By April 15 of each year, the highest-ranking executive or the board of directors must submit an electronic certification of compliance to the NYDFS. This document attests that the institution's cybersecurity program met all Part 500 requirements during the prior calendar year.
Signing the document exposes signatories to regulatory enforcement if the attestation is inaccurate. If a foreign financial institution cannot certify full compliance due to gaps in its program, it must submit a written acknowledgment of noncompliance. This submission must include a remediation timeline explaining how and when the institution will resolve the gaps.
Penalties and Exemptions
Penalties for NYDFS noncompliance frequently range from hundreds of thousands to tens of millions of dollars per enforcement action. The DFS calculates fines based on the severity of the violation, the institution's cooperation, and the presence of systemic compliance failures.
Small branches may qualify for limited exemptions based on employee count, gross annual revenue, or total assets. Even exempt entities must still adhere to core requirements, including conducting risk assessments and maintaining third-party vendor security policies.
Common Misconceptions About NYDFS Compliance
Many foreign financial institutions underestimate the jurisdictional reach and strict documentation standards of the NYDFS. Corporate counsel must address common assumptions about how global compliance overlaps with local New York regulations.
- GDPR equivalence: Executive boards often assume that meeting GDPR standards in Europe guarantees NYDFS compliance in the United States. Part 500 requires prescriptive technical configurations that GDPR does not mandate.
- Parent company umbrella protection: Foreign branches often rely entirely on their parent organization's overarching cybersecurity policy. NYDFS requires policies and risk assessments localized to the specific threats and infrastructure of the New York entity.
- Vendor liability transfer: Institutions frequently assume transferring operational tasks to a third-party vendor also transfers regulatory liability. Under NYDFS rules, the covered entity remains fully responsible for the security of its nonpublic information, regardless of who hosts the data.
When to Consult Legal Counsel
Engaging legal counsel helps protect the institution from regulatory fines when establishing a new New York branch, auditing vendor contracts, or responding to a suspected data breach.
A data breach triggers immediate legal obligations carrying severe financial consequences if mishandled. Experienced regulatory lawyers guide foreign institutions through the 72-hour reporting window, manage communications with state regulators, and shield internal compliance audits under attorney-client privilege. If your institution is preparing for an annual certification or facing a regulatory inquiry, consulting corporate and commercial lawyers in the United States helps mitigate corporate risk.
Next Steps for Foreign Financial Entities
To meet local Part 500 requirements, foreign financial institutions should take the following immediate steps:
- Review the latest NYDFS Part 500 amendments to ensure internal policies reflect current regulatory expectations regarding multi-factor authentication and executive sign-offs.
- Audit your third-party vendor roster to verify that all active contracts contain mandatory cybersecurity provisions and breach notification clauses.
- Schedule a localized penetration test and vulnerability assessment targeting the infrastructure utilized by the New York branch.



