- Foreign banks with New York branches must comply with 23 NYCRR Part 500, enforced by the New York Department of Financial Services (NYDFS).
- Covered entities must notify the NYDFS Superintendent within 72 hours of determining a material cybersecurity event has occurred.
- A designated Chief Information Security Officer (CISO) and the highest-ranking executive must personally sign an annual compliance certification every April 15.
- Home-country data protection frameworks like GDPR do not satisfy NYDFS mandates without localized adjustments.
- Unmonitored third-party vendors frequently trigger multimillion-dollar NYDFS enforcement actions.
NYDFS Cybersecurity Compliance Checklist
The NYDFS Part 500 regulation requires a cybersecurity program tailored to the risk profile of your New York branch. Use this baseline checklist to evaluate operational readiness before the annual certification deadline.
Governance and Oversight
- Appoint a qualified Chief Information Security Officer (CISO).
- Designate a senior governing body to oversee cybersecurity risk.
- Approve the written cybersecurity policy at the board or senior management level annually.
Technical Controls
- Implement Multi-Factor Authentication (MFA) for remote access to the internal network and third-party applications.
- Encrypt non-public information (NPI) in transit and at rest.
- Conduct continuous vulnerability assessments and annual penetration testing.
- Maintain offline, immutable backups of critical data.
Risk Management and Reporting
- Complete a documented risk assessment at least annually.
- Develop and maintain a localized incident response plan.
- Map and inventory all hardware, operating systems, and applications.
- Establish a vendor risk management policy covering due diligence and periodic assessment.
Scope and Limited Exemptions
Non-public information (NPI) under NYDFS Part 500 includes sensitive personal data like Social Security numbers or biometric records. It also covers confidential business information that could negatively impact the financial institution's operations if exposed.
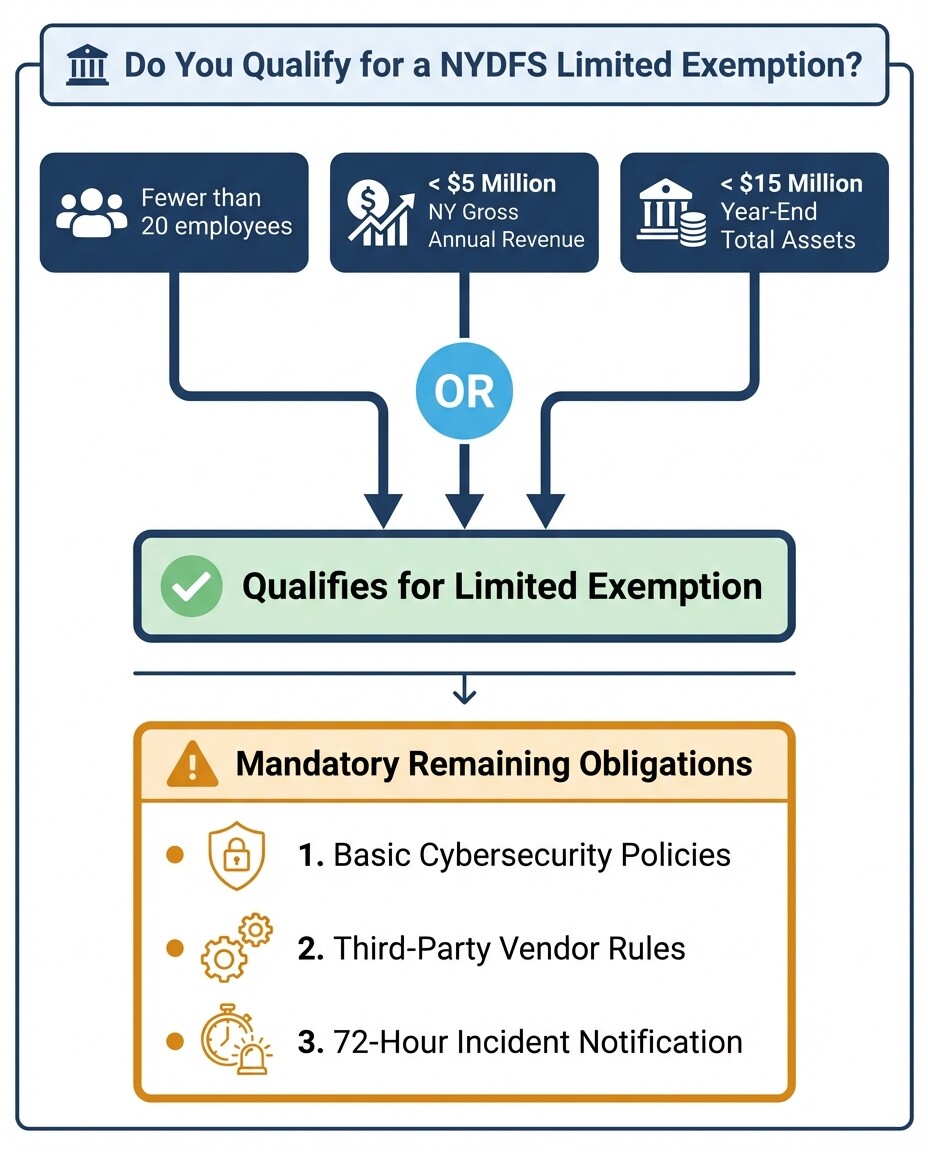
Entities qualify for a limited exemption if they have fewer than 20 employees or less than $5 million in gross annual revenue from New York operations. Institutions with less than $15 million in year-end total assets also qualify. Exempt entities must still implement basic cybersecurity policies and comply with third-party vendor rules. They are also subject to the 72-hour incident notification requirements.
Appointing a Qualified CISO
Foreign financial institutions must designate a qualified Chief Information Security Officer to oversee the New York branch's cybersecurity program. The CISO manages a localized incident response plan built for specific DFS mandates and local operations.
The NYDFS allows the CISO to be employed directly by the covered entity, an affiliate, or a third-party service provider. A foreign bank can use its global CISO for this role, provided that individual fulfills all local requirements. If an external CISO is used, the foreign entity retains full responsibility for compliance and must designate an internal senior employee to oversee the third party. The CISO must present a written report to the senior governing body at least annually. This report details the current cybersecurity posture and material risks. It also evaluates incident response effectiveness.
Your incident response plan cannot be a global corporate document. It must address how the local branch detects and recovers from attacks. The plan defines internal roles and outlines data recovery procedures. It also integrates notification protocols required by New York regulators.
The 72-Hour Reporting Rule
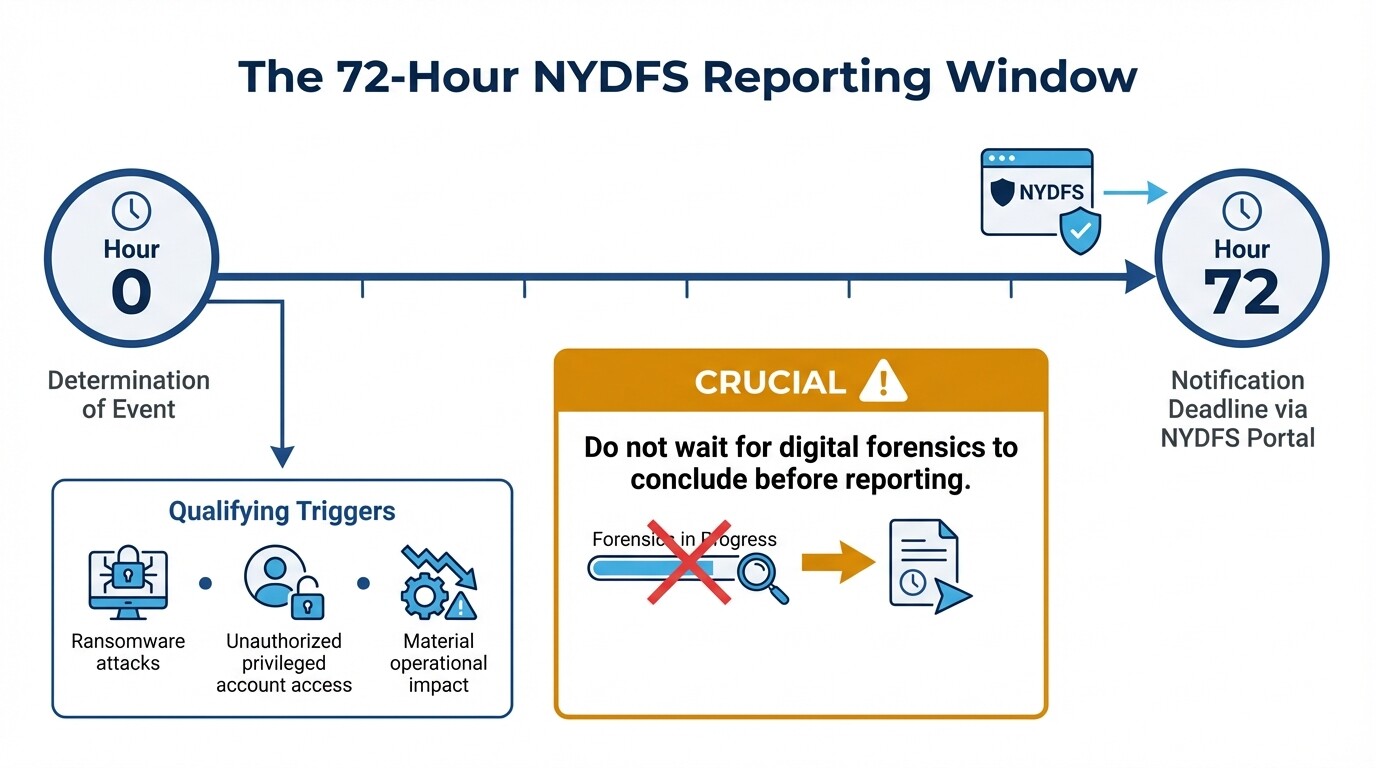
Covered entities must notify the NYDFS Superintendent within 72 hours of determining a qualifying cybersecurity event occurred. This timeline applies to incidents impacting the New York branch directly or affecting its third-party service providers.
Under 23 NYCRR Part 500, a reportable event extends beyond a confirmed data loss. Notification triggers include events that materially impact operational capability or require notice to another government body. Ransomware and unauthorized access to privileged accounts also mandate reporting. The 72-hour clock begins the moment the entity determines the event meets these criteria. Rapid internal escalation is necessary.
Filings go through the official NYDFS Cybersecurity Portal. Missed deadlines frequently result in severe financial penalties, even if no consumer data is stolen.
Managing Vendor Risk
Digital supply chain failures are a leading cause of NYDFS enforcement actions against foreign financial institutions. Part 500 requires due diligence and mandatory contractual protections. It also mandates continuous monitoring for third-party service providers holding non-public information.
Foreign entities need written policies establishing minimum cybersecurity practices for vendors doing business with the New York branch. Banks must assess the vendor's security controls before onboarding.
Vendor contracts must require the third party to use Multi-Factor Authentication and encrypt data. Vendors must also agree to immediately notify your institution of a cybersecurity event. NYDFS rules mandate financial institutions periodically reassess these vendors. Risk management is an ongoing process rather than a one-time onboarding checklist.
Meeting Certification Deadlines
Every covered foreign financial institution must submit an annual Certification of Material Compliance to the NYDFS Superintendent by April 15. The designated CISO and the highest-ranking executive must personally sign this document, assuming liability for the program's effectiveness.
By signing, executives legally attest that the New York branch's cybersecurity program fully complied with Part 500 during the prior calendar year. Institutions not in full compliance must submit a written acknowledgment identifying specific deficiencies and outlining a remediation timeline.
Documentation supporting the certification must be retained for five years and made available for inspection during regulatory examinations. Filing a false certification can lead to enforcement actions for fraudulent misrepresentation alongside the underlying cybersecurity failures.
Mapping NYDFS Part 500 to GDPR
GDPR focuses on consumer privacy and data rights. NYDFS Part 500 protects the operational security and stability of the financial system. Aligning the two requires mapping shared controls like encryption and access management while addressing DFS-specific governance rules.
Foreign banks cannot port European or Asian compliance frameworks directly into New York. GDPR compliance provides a foundation for data mapping and encryption, but NYDFS imposes prescriptive technical mandates absent in principles-based frameworks.
| Requirement Area | GDPR (European Union) | NYDFS Part 500 (New York) |
|---|---|---|
| Primary Focus | Data privacy and consumer rights. | System stability and defense against cyberattacks. |
| Breach Notification | 72 hours to data protection authority. | 72 hours to NYDFS Superintendent. |
| Authentication | Emphasizes appropriate technical measures. | Mandates MFA for remote and administrative access. |
| Executive Liability | Penalties levied against the corporate entity. | Requires personal attestation by executives. |
Common Misconceptions
Foreign executives often believe their home country's regulatory compliance satisfies New York state requirements. Understanding common pitfalls prevents enforcement actions.
- Global policies cover local branches: International banks often use a centralized global cybersecurity policy. NYDFS requires policies tailored specifically to the localized risk assessment of the New York branch.
- Large vendors are exempt: Banks sometimes assume large cloud providers are exempt from third-party risk management rules. NYDFS holds the covered entity responsible for the security failures of any vendor, regardless of size.
- Forensics must finish before reporting: Institutions sometimes delay the 72-hour notification while waiting for digital forensics to confirm the scope of a breach. NYDFS expects notification upon the determination of a qualifying event, even during early investigation stages.
When to Hire a Regulatory Lawyer
Legal professionals with expertise in US financial regulations help establish New York branches and manage cyber incident responses. Counsel ensures internal policies align with state law and protects privileged communications.
Foreign institutions benefit from consulting a regulatory attorney immediately upon detecting a cybersecurity anomaly. This secures attorney-client privilege during the forensic investigation. A lawyer helps determine if an incident crosses the threshold for the 72-hour reporting rule and guides executives through the liability implications of the annual certification. To assess your compliance posture, consider reaching out to experienced corporate and commercial lawyers in the United States to conduct a gap analysis of cross-border operations.



